DPRK Fake IT Workers Fraud Playbook
DPRK Fake IT Workers Fraud Playbook
Summary
Following the first article on the DPRK fake IT workers infrastructure, we wanted to write a separate article about the cybercrime ecosystem, which is unique in that it combines a persistent conglomerate of companies with a large number of North Korean workers. In this article, we will present the methodologies used in our research on this subject.
Understanding the environment around fake IT workers
As we saw in our research, North Korean IT workers use their own terms to describe the elements of the infrastructure shown below.
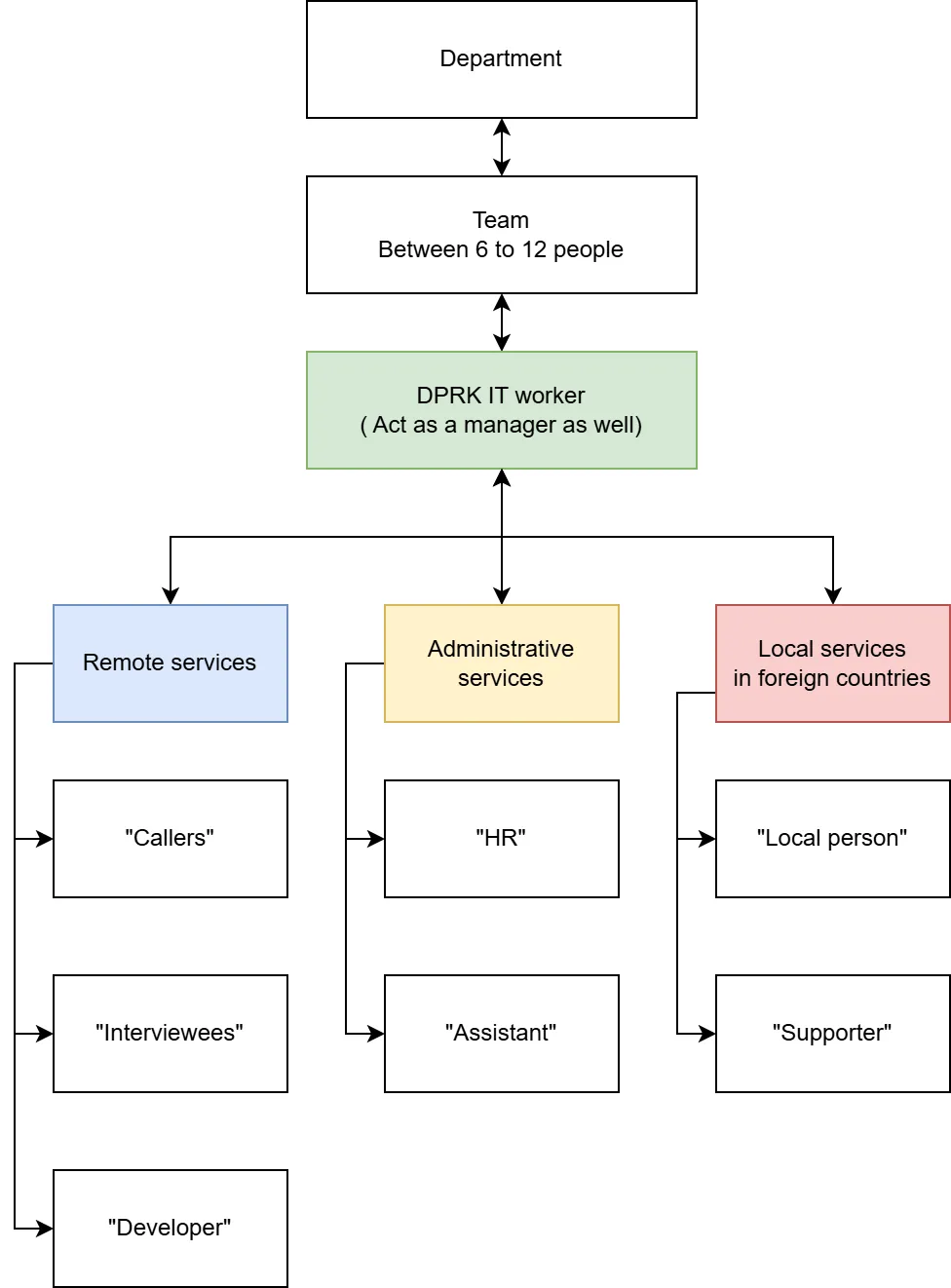
Mainly for the remote services part, we could observe a cluster of developers in Iran, Syria, and South Africa who are regular citizen that accepted to be hired following a proposal on LinkedIn by North Korean IT workers, followed by a change of application to discuss on WhatsApp with the newly hired person. LinkedIn is widely used as a first approach for new hires and to initiate first contact within the targeted countries, which vary depending on the job offer.
The technique of the first approach may vary depending on the North Korean IT worker; they don’t have a defined process and seem free to use their own methods.
Figure 2: Table and definition of each role within the cybercrime structure
For the local employees who appear to be mainly within the US, they are targeted on LinkedIn, likely in specific position as we could see most of the targeted “Local person” or “supporter” are drivers, plumbers, freelancers, and probably more jobs. The tariffication to obtain a fake identity is 250 US dollars prepaid, and “local persons” can introduce their friends as well to give their identity to DPRK IT workers.
Links with non-state backed cybercrime
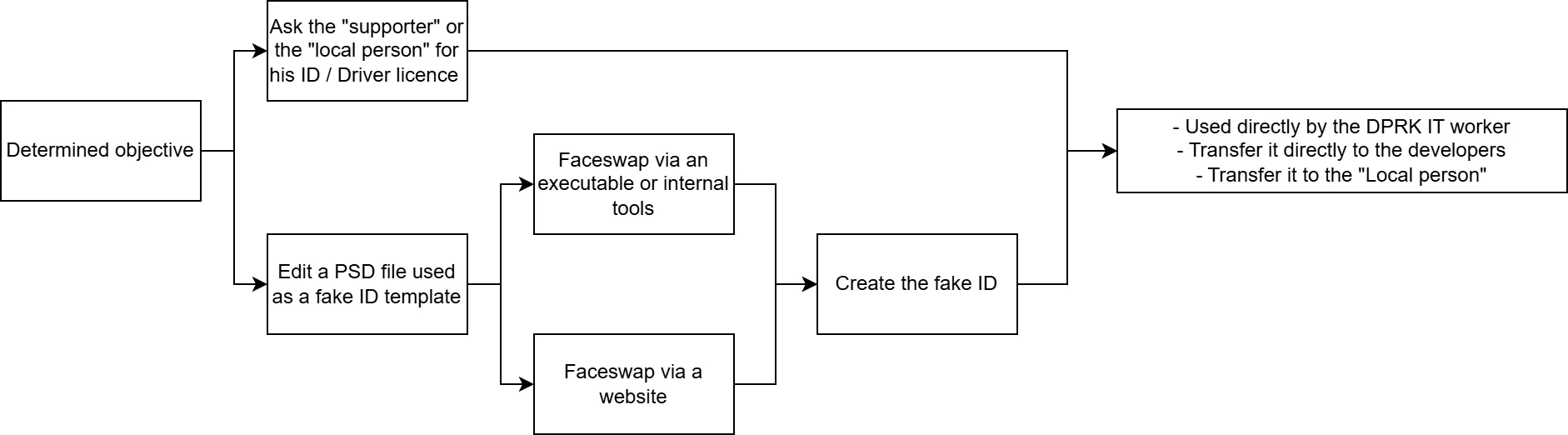
As we could see, DPRKIT workers use data brokers to obtain fake identities, which is an important step toward mastering the verification bypass on job offer websites, social medias and background checks during the interview process. The DPRK IT worker is the only one who manipulates the .PSD files and applies modifications to them.
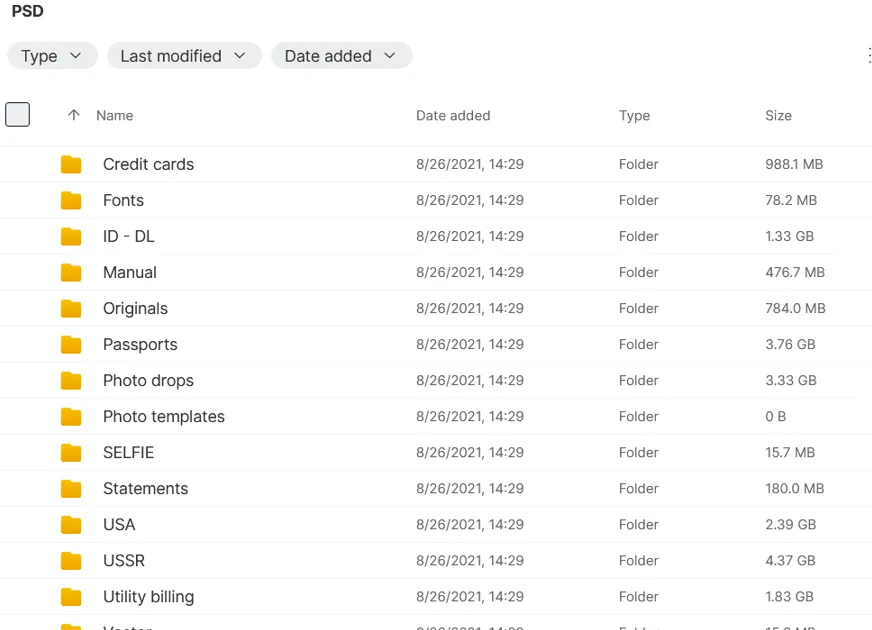
With these .PSD files, we observed that the developers acknowledged using fake identities to swap identities between interviews with their consent.
During our investigation into stealer logs, we observed that DPRK IT workers had developer-level access to the U.S.-sanctioned hosting service ‘Funnull’. As we can see, they maintained the infrastructure and performed fixes on “Goedge CDN,” an open-source solution for building their own CDN and WAF.
Financial analysis
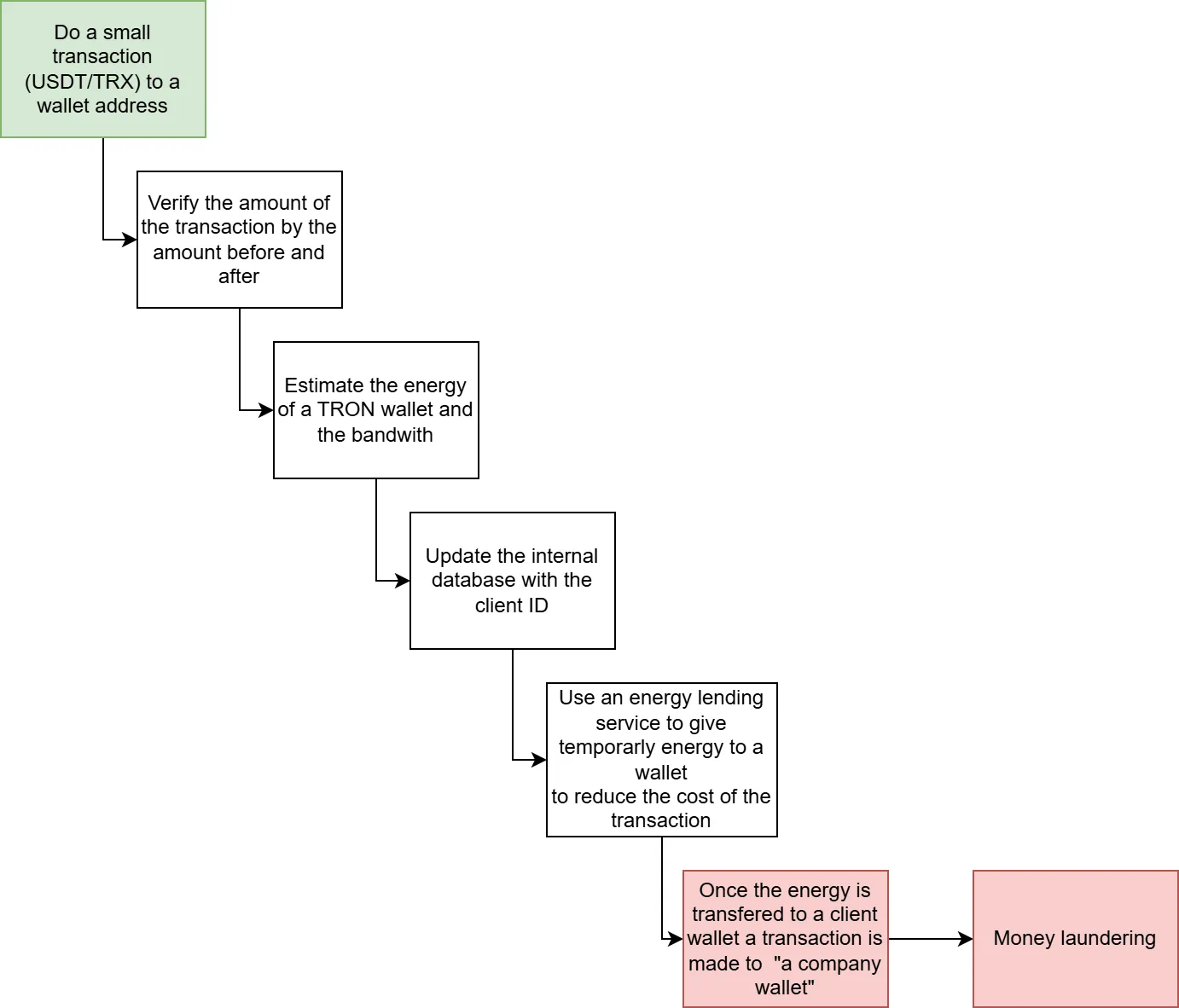
As we could see during our analysis, we assessed that DPRK IT workers are using similar techniques as Blackbasta to do cash out, but this time with Tron to USDT(Tether) to do cash out on a wallet named “company” or maintain their infrastructure.
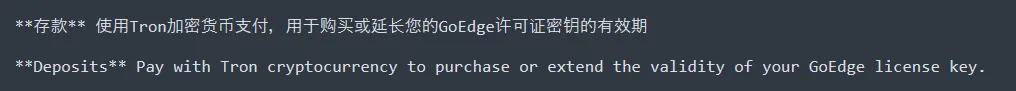
It seems they put a lot of effort into reducing and optimizing energy consumption; for that, we found traces of automated transfers via Tron (TRX).We could see on the stealer log this specific process
Sources
Hudsonrock (for the stealer logs)
https://home.treasury.gov/news/press-releases/sb0149
ANNEX 1 – “Localperson” / “Supporter” targeted locations
ANNEX 2 – Assessed profiles












































.avif)




















.webp)

