Inside the Cyber Infrastructure Behind DPRK Fake IT Worker Operations
Inside the Cyber Infrastructure Behind DPRK Fake IT Worker Operations
Summary
After our article about the internal infrastructure of theDPRK fake IT workers, we wanted to document a network that we believe that it’s used for their offensive operations as a lab for various purposes that we can’t give because at this time we don’t know what their main mission within this infrastructure part are. Over the time they gained maturity and learned how structure and industrialize their offensive operations.
Infrastructure assessment
During our research we could assess with moderate confidence these four distinct networks. (see Annex A)
- 192.168.213.0/24 [ AI ]
We chose to merge it with the other networks because they use Kibana and AI search and with low confidence we saw the usage of Gradio. - 192.168.140.0/24 [ AI, DEVOPS and NPM development infrastructure ]
We chose this description because we could observe the usage of Verdaccio and traces of NPM packages within the URL’s visited by the assessed actors. - 192.168.47.0/24 [ Network ]
We chose to merge it with the other networks due to the presence of the same actors in the confirmed range 192.168.140.0/24. - 192.168.35.0/24 [CI / CD]
We chose to merge it with the other networks due to the presence of the same actors and the same servers used on both networks 192.168.35.0/24 and192.168.140.0/24 which are drone CI and Gitea.
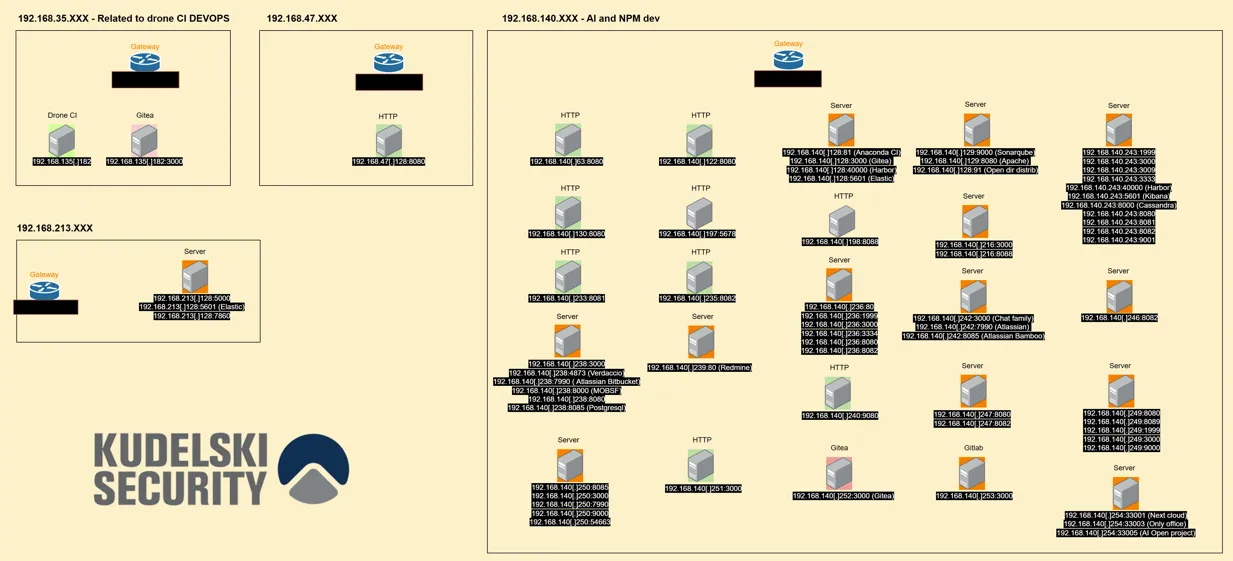
This specific infrastructure is not like the previously assessed one, due to the number of services that each machine serves which is greater than that on other networks and due to the presence of MOBSF which is used as an offensive security tool. It seems that they have machines with more allowed resources.By using the identified servers, we can’t reconstitute their development workflow and what they are doing inside of these networks. Even with low confidence, because as we don’t have a clear view of what is the objective here, it could be either a testing infrastructure or a pre-production environment. Based on the threat actors activity, we can say that it is likely related to an offensive environment.
During our research on the external infrastructure, we saw that many public IP addresses belonging to AstillVPN, VPS providers or residential proxies overlap with hacking campaigns led by North Korean actors. Even when these public IP addresses are related to North Korean IT workers because they sometimes share the same infrastructure and exit nodes, as multiple cells seem to converge into the 192.168.91.0/24 network range. This allows them to avoid being flagged while applying for job offers or compromising companies. To bypass country-based detection, they mainly chose VPS servers hosted in Europe or in North America.
Infiltrating companies can be considered as an initial access technique that can lead to prepositioning techniques for espionage or disruptive operations. During our ongoing research, we observed that they attempted to apply for OT related positions, roles within the Energy sector, and also placed specific markers in the Aeronautics sector and defense sectors mostly in the US and across EU countries.
Main pivot point to the development infrastructure
Following the previous article about their infrastructure we wanted to retrieve more network linked to the fake IT workers, so we took the most used IP internally as mentioned on the chats from “IPmsg”.
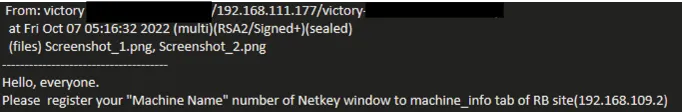
Since we know that they all had to register on this server,we were able to pivot to other public IPs that have not yet been flagged as belongingto Fake IT workers by using the “domain” field within Hudsonrock which can bealso used for private IPs.

Source
Hudsonrock (for the stealer logs)
https://lazarus.day/search/?q=npm
https://www.recordedfuture.com/research/purplebravos-targeting-it-software-supply-chain
https://www.sentinelone.com/labs/contagious-interview-threat-actors-scout-cyber-intel-platforms-reveal-plans-and-ops/
Annex A
Here you will find an array with the infrastructure elements identified within this group of networks.












































.avif)




.png)














.webp)