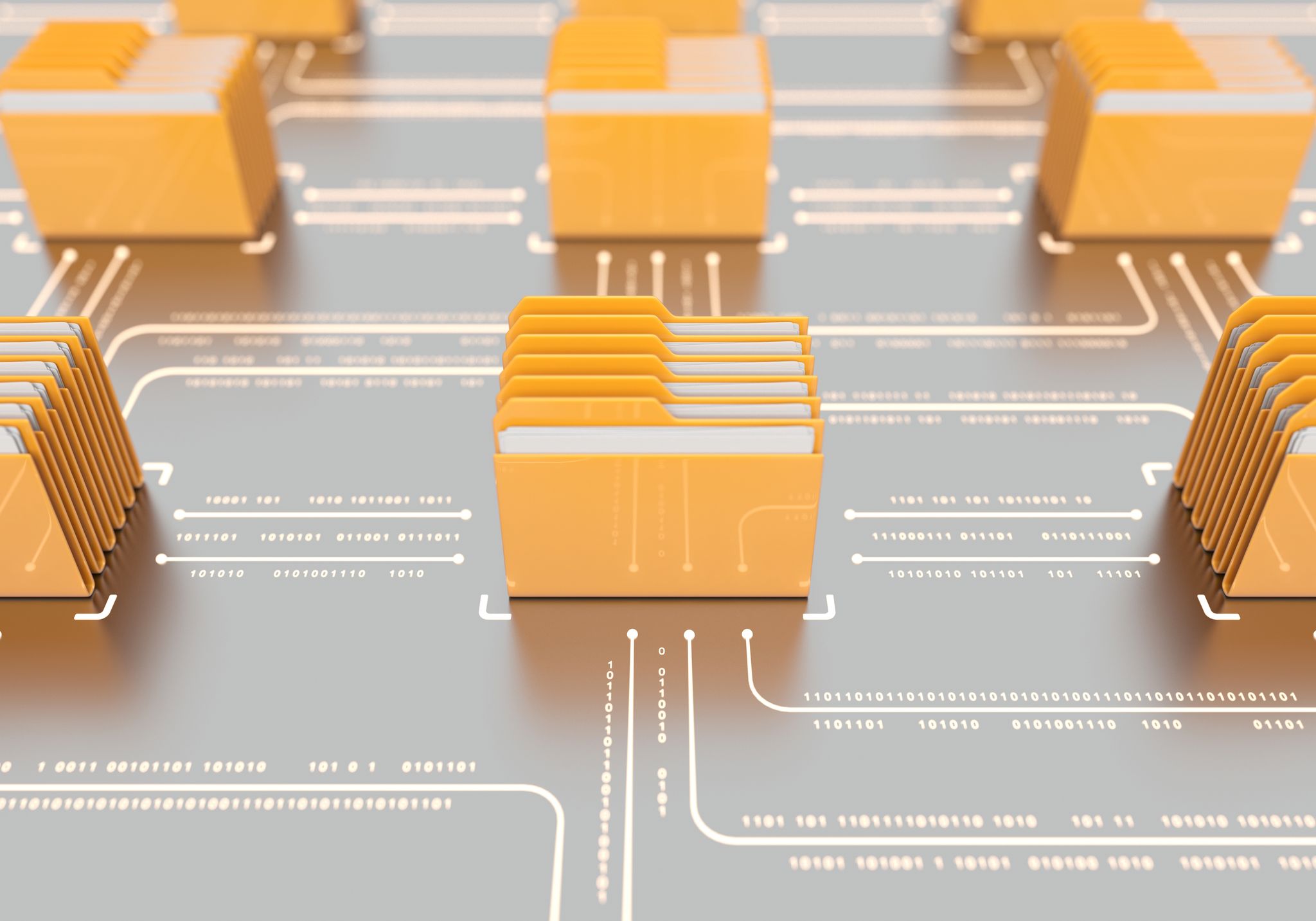
Technology Implementation and Migration
Optimize your cybersecurity investments and drive greater business efficiency with our expert-level solution implementation and migration services. Find out more about Technology Implementation and Migration.

Proper Implementation
From product installation and migration to tech-on-tap services, firewall optimization, and service tune-ups, our highly certified field engineers provide everything you need to ensure your security technologies function correctly and integrate seamlessly into your current IT infrastructure. The implementation team that plans and deploys your implementation or data migration consists of highly skilled engineers with long, in-depth experience.
Working on your premises or remotely, their outstanding technology fluency and business acumen enable them to resolve any issue as it emerges, ensuring your new security solutions are problem-free and effortlessly tuned, implemented or migrated.
A History of Trust
-
Top-ranked
We are recognized throughout the security industry for our wide-reaching implementation and data migration capabilities.
-

Powerful Partnerships
Our strong relationships with leading technology manufacturers help us deliver well-tailored solutions that dovetail with client needs.
-

Relationship-Based
Our collaborative approach gives our engineers an intimate understanding of your business and the ability to work closely with your internal resources.
Big-Picture Planning, Detail-Oriented Execution
-
Optimized Performance
We ensure your new technologies deliver the best possible performance by being installed properly and configured to meet your expectations.
-
Continued ROI for Legacy Systems
New solutions are designed to integrate seamlessly into your existing cybersecurity environment.
-

Data Continuity
All your historic data and information is effectively and completely migrated onto new tools.
-
Updated Versions
Our engineers make sure your existing technologies are kept up to date with current versions and features.
-
Documentation and Training
We provide the resources and know-how to keep your new technologies maintained over time.
Featured Resources
Kudelski Security Recognized as a Notable Vendor by Gartner in Latest MSS Magic Quadrant
IT & Security leaders are looking for trusted security partners who can help them increase visibility of assets, reduce complexity, and address critical talent shortage.
Our services cover all cloud environments so that wherever you are on your cloud journey, we’ve got you covered.