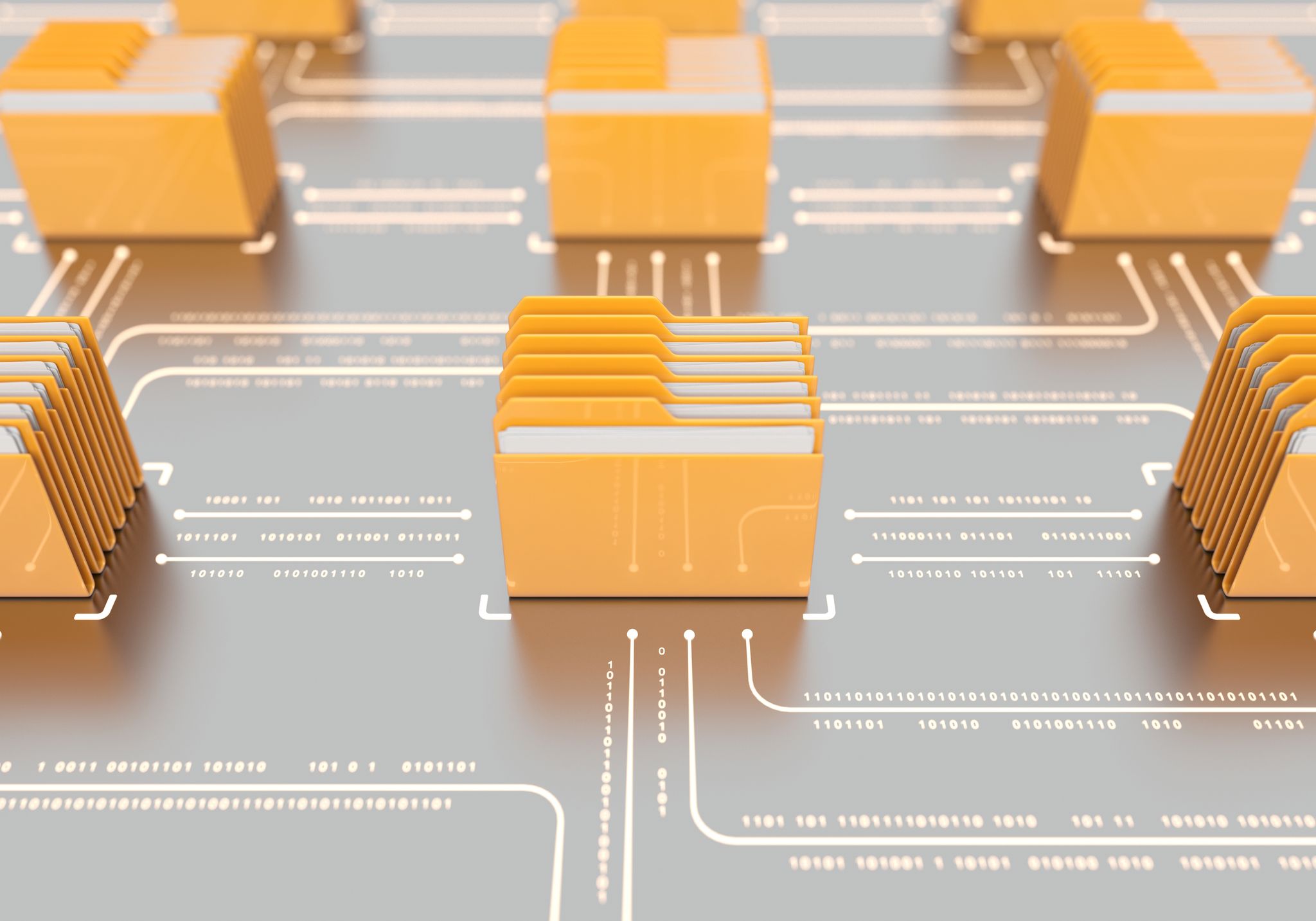
Threat Monitoring & Hunting
The CFC delivers superior visibility into threats and adversaries and greater contextual relevance of an ever-shifting threat landscape. We hunt and detect threats faster, 24x7, and respond more adaptively to contain and remediate.

Full-Spectrum Visibility; Human-Led Threat Hunting
We can reduce detection time from days to minutes. We gather security data from across your environments (traditional IT, cloud, hybrid, OT/ICS), and automatically fuse it with threat intelligence to generate a rich, contextualized view of your security landscape. Our security analysts and hunters will also uncover suspicious behavior – advanced, signature-less threats in your environment. They will instantly activate your incident response plan and give clear, actionable remediation steps or take the action on your behalf.
Superior Service
-
Dedicated Guidance and Support
Our expert Cyber Fusion Center analysts provide skills and actionable remediation recommendations that extend your internal capabilities.
-
Proven Processes
A tried and tested four-phase onboarding and best in class security operations processes ensures you get the scope and service you require.
-

Security Everywhere
We offer global reach, multilingual support for our cyber intelligence platform, and operations in the United States and Switzerland.
Strengthen Security Posture
-

Extend your security team
Our expert Cyber Fusion Center analysts provide guidance and support to your security team.
-
Reduce Dwell Time
Drastically reduce the time to detect and respond to threats through contextual intelligence automatically fused into our analytics process and tools.
-

Control Expenses
Optimize cost predictability and scalability of security operations.
-
Comprehensive Visibility
Real-time alerts and reports delivered from the MSS Client Portal provide comprehensive visibility of your security posture across on-premise, hybrid, cloud, OT/industrial control systems, and IoT environments.
-
Achieve Compliance
Meet your regulatory and compliance requirements.