Cyber Fusion Center
CISOs and security operations leaders need relevant intelligence, contextualized data, and comprehensive threat response plans. Our Cyber Fusion Centers (CFCs) meet that need with an approach designed from the ground up to address the modern cyber threat landscape. Find out more about our Managed Detection and Response services, delivered from our CFC.

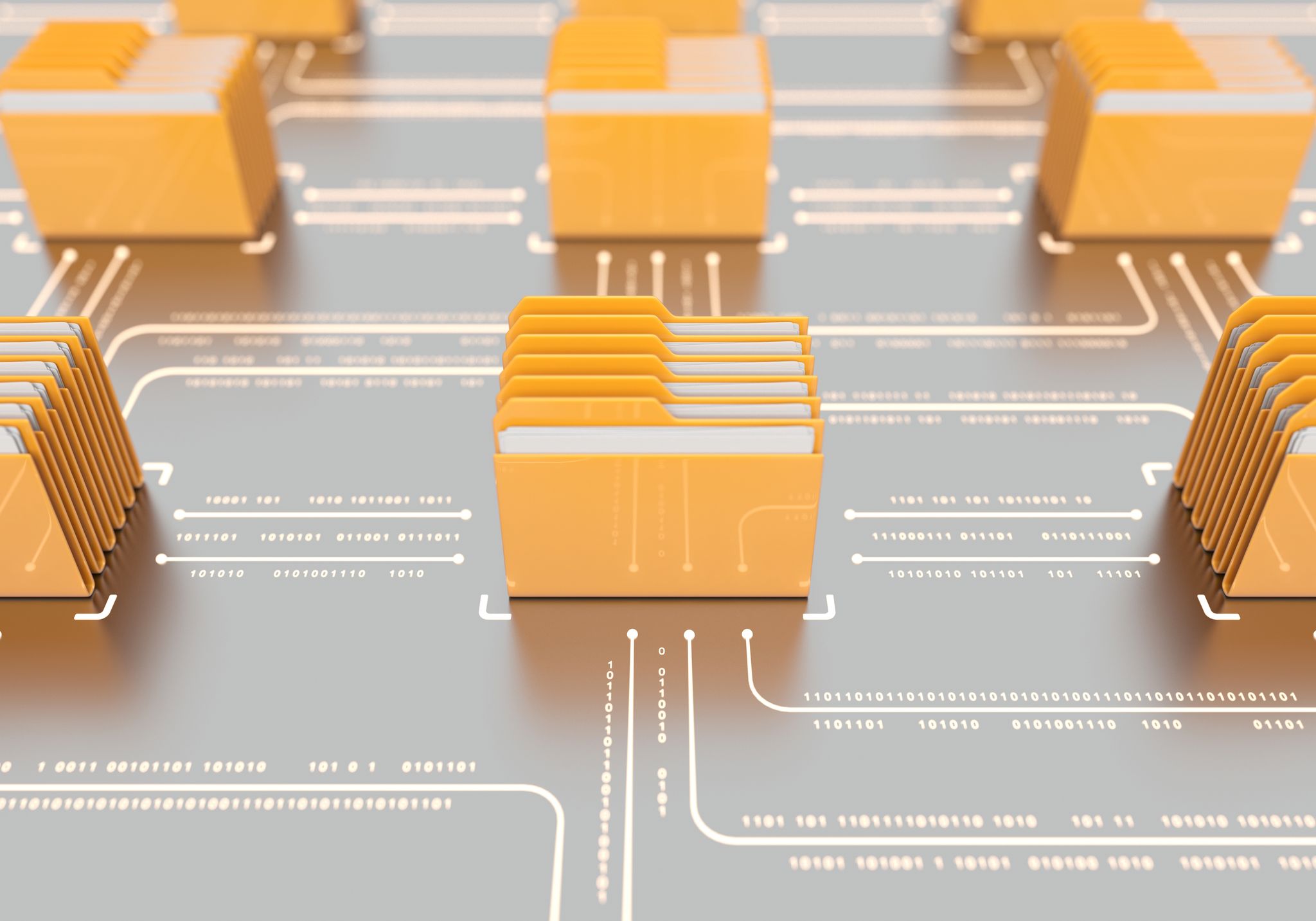
We Protect Your Data – Wherever It Resides
Our Cyber Fusion Centers located in Europe and the United States deliver unified visibility across technology landscapes: on premise, cloud, hybrid, OT/ICS. Wherever your data resides, we can protect it. Using a non-linear approach to the attack kill chain, we combine robust use case frameworks, purpose-built tools, and cutting-edge technologies with rich business and contextual data to detect threats faster, respond more effectively, and reduce risk.
We Focus on Outcomes Not on Managing Technology
-
Attack Disruption
The traditional focus is on the breach stage of the attack kill chain. We take a non-linear approach that mirrors the way attackers move so attacks are interrupted at progressively earlier stages for rapid containment.
-

Context and Analytics
Leveraging our in-house R&D capabilities, we contextualize findings and inject them into a custom-built analytics platform that reduces detection time and even uncovers threats in the pre-breach phase.
-
Fused Cyber Intelligence
We fuse technical data with relevant threat, industry, and business intelligence to provide detailed, tailored cyber threat reports with recommendations on quick, effective responses.
Radically Effective Security
-

Detect and Defend
The Cyber Fusion Center correlates, enriches and analyzes massive amounts of data to accurately learn the habits and methodologies of attackers, which we use to identify indicators of attack (IoC) and the latest tactics, techniques, and procedures (TTP).
-
Protect Operations and Reputation
Our approach and capabilities allow us to minimize the impact of a breach through faster detection and response, or identify and stop attacks before they actually breach the network.
-
Expert Guidance
The CFC Threat Analysis team filters false alerts, collects forensic information, and prioritizes remediation activities.
Featured Resources
Kudelski Security Recognized by Gartner in 2019 MSS Magic Quadrant
IT & Security leaders are looking for trusted security partners who can help them increase visibility of assets, reduce complexity, and address critical talent shortage. Our services cover all cloud environments, so that wherever you are on your cloud journey, we’ve got you covered.