Penetration Testing Services
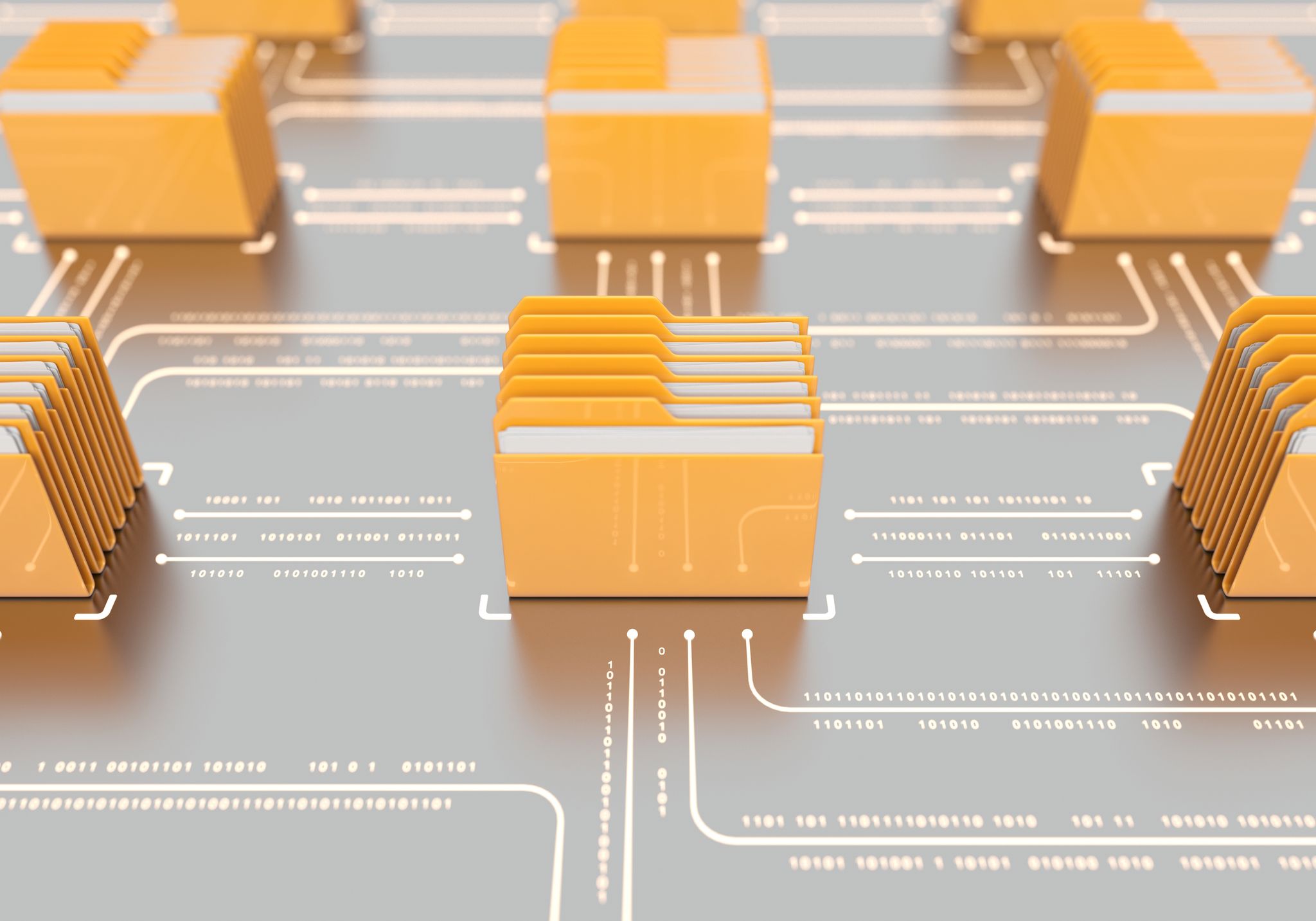
As cyber-attacks become more frequent, targeted and sophisticated, a proactive, periodic approach to validating security controls and identifying vulnerabilities can reduce the likelihood and severity of an attacker successfully gaining entry into your network.

The Best Defense Is a Good Offense
Today’s connected enterprises can’t afford to wait for an attack before they tune their security defenses. Our suite of Penetration Testing Services and Offensive Security services helps you expose and remediate vulnerabilities before an attacker has a chance to exploit them. We tailor our penetration testing service and team engagements to your unique security needs in order to assess and strengthen your organization’s security posture.
The Kudelski Security Advantage
-

Trusted Security Pentesting Partner
We’re trusted by the world’s largest enterprises to uncover hidden vulnerabilities in their digital assets and infrastructure.
-
World-Leading Security Experts
Our security engineers, developers, and leaders include the world’s foremost experts on everything from cryptography to penetration testing.
-
Committed to R&D
We invest millions annually in research, development, and testing to ensure customers receive the most in-depth security services available anywhere.
-

Experience Matters
Our consultants and penetration test engineers have years of highly technical experience and are thought leaders within the security community as well as having attained numerous security and compliance certifications.
Penetration Testing Services for Networks, Hardware & Applications
-

Vulnerability Assessments
Understand your current state of security with an automated network scan that can be used to meet compliance and audit requirements or validate patching and hardening.
-
Web Applications
Identify vulnerabilities, test business logic and access controls and search for hidden fields, values or functionality in internal or external web applications.
-
Applications
Identify vulnerabilities, test business logic, access controls, etc. in standalone software applications.
-
Hardware
Identify plant equipment, product hardware, and IoT devices that may be exposing sensitive data, allowing unauthorized access, or manipulation of device commands.
-
API/Web Services
Perform end-to-end security analysis on architecture design, development and penetration testing practices for middleware that connects interfacing system components with the infrastructure.
-
SCADA
Determine if a device is exposing sensitive data, allow for unauthorized users to gain full access to a system, or manipulates device commands. This includes OT security testing for industrial plant equipment.
-
Mobile Application
Evaluate data transmission and server-side infrastructure controls and identify backend service vulnerabilities for end-user mobile apps.
-

Networks
Get deeper insights into systemic issues spanning systems, domains or security zones with a goal-based network test that simulates current threats.
Offensive Security Team Engagements
-

Red Teaming
Uncover the avenues of entry into your network and learn how your network, security controls, alerting and monitoring systems will stand up to an attack. Our red team will attempt to evade detection across fixed and wireless networks, applications, phishing attempts and, in some cases, in the physical environment.
-

Purple Teaming
Improve security operations and incident response capabilities within your own environment, using your own tools. Our red team will work with your security team to design and deploy the campaign to test your defenses across fixed and wireless networks, applications and, in some cases, the physical environment.
Coordinated Threat Exercises
-
Are penetration testing activities dangerous for our infrastructure?
While all penetration testing has some level of risk, it is far more dangerous to leave your infrastructure untested. Our team of seasoned professionals will help you scope your testing projects, identifying critical systems and establishing rules of engagement to manage those risks, such as testing in staging environments or eliminating techniques known to have a higher chance for negative impact.
During testing we will be in constant communication with you, and will do our best to make sure your business is unaffected. Last but not least, at least two people of our team are always reachable throughout the test in case of emergencies.
-
What if you break something in the pentest?
Because of the nature of the tests we perform, there is always the risk of service disruption. However, we pride ourselves on an extremely high success rate, which we attribute to the diligent scoping and extra precautions we take during the engagement. Further, we keep track of all activities performed throughout the engagement and leverage a testing methodology that limits the potential impact on systems or resources.
-
What about confidentiality?
A non-disclosure agreement is signed between the parties to protect confidentiality. We limit the use of client data to the bare minimum necessary to produce a detailed technical report on any discovered findings. Any client data processed during testing is kept safely on encrypted storage and wiped after the engagement is over.
-
How often should you perform penetration testing?
Penetration testing should be performed on a regular basis to ensure more consistent IT and network security management by revealing how newly discovered threats or emerging vulnerabilities may potentially be assailed by attackers.
We recommend running tests at least annually or whenever:
- New network infrastructure or applications are added
- Significant upgrades or modifications are applied to infrastructure or applications
- New office locations are established
- Enterprise-wide end user policies are significantly modified
- Following a cybersecurity incident that compromised network security controls
-
What is the added value of offensive testing for my company?
A penetration test is a drilling exercise that allows a customer to test their resilience and responsiveness to technical threats. It helps discover how technology translates into institutional risk. In addition, it will also help you to clarify if, in case of a real attack, you will be able to detect it on time and avoid nasty surprises such as your company’s name found in the ‘Under Cyber-Attack’ news section.
-
What is the end result of a penetration test?
Penetration testing provides a clear picture of the risks in your environment that a skilled threat actor could exploit. The recommendations provided within our penetration test reports, if followed, will significantly enhance your organizations’ cybersecurity posture.
-
What is the difference between vulnerability assessment and penetration testing?
A vulnerability assessment (VA) provides you with a list of vulnerabilities that an attacker might leverage in an attack. Many exploits have numerous dependencies that must exist for the attack to be successful. That level of validation can only be provided through penetration testing. During penetration testing, a skilled engineer understands the conditions required for each exploit to work and carry out the attack safely, thus limiting system impact.
-
What is red teaming vs penetration testing?
Penetration testing is a horizontal assessment that highlights the clients’ attack surface, while Red Teaming is an objective-based vertical assessment. Further, Red Teaming typically utilizes more aggressive techniques such as social engineering or close access operations to achieve their goals while evading detection from the client’s security team.