Centre de ressources Kudelski Security
Bienvenue dans notre centre de ressources. Vous y trouverez des brochures, des fiches techniques et des vidéos sur nos services et solutions de cybersécurité. Recherchez dans la bibliothèque par sujet ou par catégorie.

171 Results

etude de cas
Cybersécurité : renforcer la sensibilisation et la confiance grâce à un centre de cyberdéfense à la pointe de la technologie

Etudes de cas
Endiguement et remédiation rapides face à une cyberattaque de grande envergure

ModernCISO Guide
The Four-Step Framework for Managing Insider Risk
A practical guide to help you mitigate insider risks and build a stronger data security program.

Infographics
6 Key Considerations for Good Insider Risk Management
A few principles to keep in mind while you build or improve your insider risk function.

Infographics
15 Practical Tips How To Prepare Your Environment For A Security Incident
As a security leader, you’ll know that good cybersecurity incident response requires good foundations, open communication, and good teamwork. And the responsibility to make it happen is yours.

Playbook
Ransomware Response Playbook
Kudelski Security’s comprehensive seven-step approach to incident response.
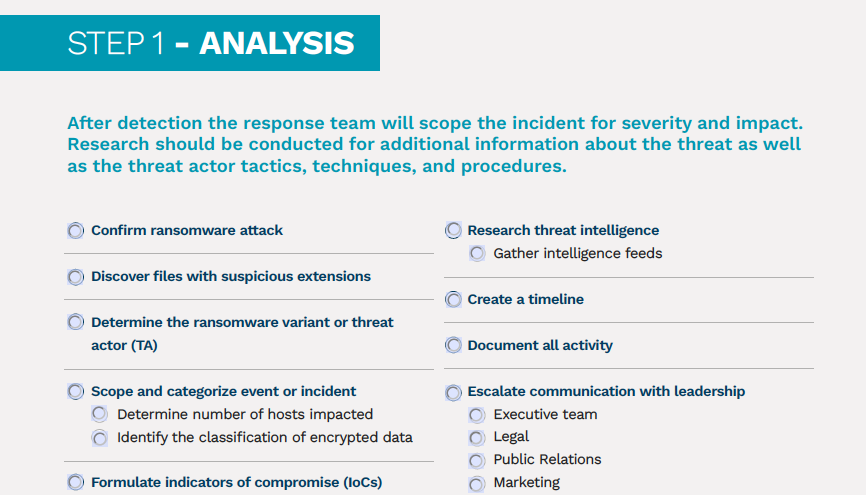
Checklist
Ransomware Rapid Response Play Cards – What to Do in the First 24 Hours
Our Ransomware Rapid Response Play Cards is a checklist to guide you through the first 24 hours of a breach.

Webinar, Webinars
Common Pitfalls Every C-Level Should Know About – Stories From Our Incident Response Team
Kudelski Security's Incident Response team discusses the tough challenges modern enterprises and C-Levels face today when it comes to managing a crisis. At the top of the list: How to identify the visibility gaps, how to respond faster, and how to respond better.



